Hi,
unfortunatly this feature uploads personal information in the internet without giving the ability to review them before or remove it later… That really sucks.
Maybe exclude everything related to WEBDAV shares and similiar remote locations from the logs or at least give a bold warning when you tell people to use this program and provide alternative ways to manually grab the logs?
I now gotta change some passwords.
Well, thanks.
Privacy
While the contents of hastebin.com are not directly crawled by any search robot
that obeys “robots.txt”, there should be no great expectation of privacy. Post
things at your own risk. We are not responsible for any loss of data or removed
pastes.
You should be careful when uploading some logs, as they may have access passwords
in them. It is your responsibility to ensure you do not have personally identifiable
information or passwords in your pastes before posting them.
Use
Please see Wiki - OSMC for more information on how to use this.
BTW that link doesnt work.
Your logs are not publicly visible.
No need to change any passwords.
But of course they are. You just need the link, but as they are generated it can be guessed. Anyone can write a script that tries out urls and captures the response when its different from “not found”.
Also if the logs are not transmitted encrypted they can allready be sniffed by MITM.
IMHO it’s already a huge flaw that the passwords are stored as plain text in the (dav) URL.
And then if I had not checked the log manually for those things, i would have just pasted the link here publicly in the forums as everyone else does.
Also nobody should want his passwords stored in plain text indefinatly on some (web-)server…
Kodi censors passwords
If you added the source via Kodi and it leaked a password then it may be a Kodi bug
Re guessing URLS, if one does that, they earn themselves an IP block for a few hours. It is rate limited and the URLs are not easy to guess. Details are rarely leaked and when they are usually concern NATed devices and cannot be personally tied to accounts. There is little incentive to harvest these logs
Logs are not stored indefinitely either.
Re non encrypted transmission: we can make Pastebin SSL based in future and will, but is your WebDAV share using SSL?
2 Likes
I’m not sure about that, been a while since I set it up. Does that matter for the password storage?
The log prints the sources.xml and that contains the paths to the webdav shares. davs://user:password/path Could be easily exluded or masked with a regex on the logfile though.
Well, thanks for relaxing my paranoia anyway 
There was a regression where passwords could leak in earlier builds.
sources.xml shouldn’t contain passwords, that’s what passwords.xml is for. A quick Kodi Wiki search didn’t turn up much but it should look like this [code]
smb://192.168.1.10/
smb://User:Password@192.168.1.10/
[/code]
1 Like
just recreated the webdav source in osmc, and again it has the user:password in the path in the sources.xml
P.S. yes it is httpS
If this is the case, then your issue is with Kodi and how it handles passwords for webdav in it’s sources.xml file. You should address the issue with them. You are adding these sources by manually editing sources.xml yourself? Or by adding the source via the Kodi GUI?
Via the GUI.
Havin the passwords in the sources.xml wouldnt be a problem if it wasnt leaked by grab-logs. As I understand this not a KODI but an OSMC tool?
In the normal kodi.log it does not reveal the username and password, instead it shows the paths as davs://USERNAME:PASSWORD@…
EDIT: last sentence is only half true, there is also a lot of lines that contain the real credentials 
It’s not being leaked by grab-logs. Look at your own ~/.kodi/userdata/sources.xml. If they are visible there, then it is Kodi that is leaking your creds, just as @sam_nazarko stated in post #4 of this thread.
well by leaking i meant, making it available online.
It wouldnt bother me that the credentials are in one (sources.)xml and not in another (passwords.xml) as long as it stays on the same machine.
Also I would not expect a logfile uploader to reveal my paths either…
Thats my point. Don’t tell people to use it then or give them a warning at least.
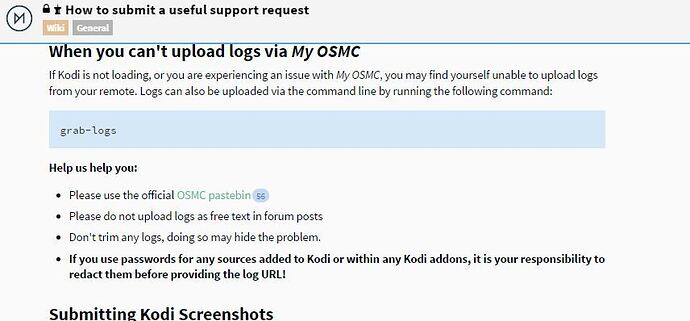
Documentation edit inbound.
It would take very little effort to edit sources and passwords.xml to correct the problem but…
You should really report this BUG to the Kodi devs
Ok can you point me to where to report it?
Also where should the passwords.xml be? Quick googling says userdata folder but it is not there.
And how can I redact my passwords from the uploaded log?
Report it to the Kodi forum, you can create passwords.xml in userdata, I posted an example earlier. You’ll have to talk to @sam_nazarko about the uploaded logs however I do know they are deleted rather quickly
http://trac.kodi.tv/
Copy paste the text in the resulting URL into a new paste.osmc.io page and do your redacting. Provide the new URL.
I’m certain your next complaint will be that your creds have still been uploaded to the paste server.
Our answer, do it all yourself. Gather the logs, make redactions, provide using some method that does not require us to download them, and do not paste the log in it’s entirety on the forum. How you do all that is completely up to you. Enjoy!
Just found this bug in the kodi tracker: Issues · xbmc/xbmc · GitHub
it’s even 2 years old sigh
For now I will just delete my webdav sources, dont really need them on Kodi anyway.
Of course I do it myself now. Would be cool if you could also provide instructions for that as well in the wiki.
Only knew where to look after running grab-log and looking through the result.
Thanks!