First of all, sorry, if this is a false positive, I’m not very familiar with the rootkit hunting yet.
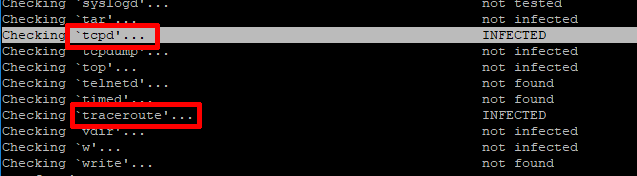
I have just re-installed my osmc with version 2018.03-2, and tested it with chkrootkit version 0.50.
It actually gets 2 hits, traceroute and tcpd.
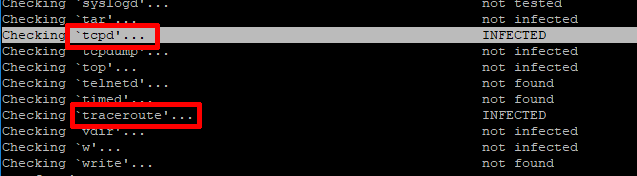
I’ve read, that tcpd tends to report false positive with the chkrootkit, but after I reinstalled the traceroute with the command
apt-get install --force-reinstall true traceroute
the INFECTED status was gone for that.
Do I have to worry about the cleanliness of the freshly installed system?
Run a single test for tcpd and traceroute.
If you get no ‘INFECTED’, then this is probably the issue: https://www.linuxquestions.org/questions/linux-security-4/chkrootkit-tcpd-521683/page2.html#post5788733
Sam
Actually the single test brought the same result for traceroute. I’ve extra done it before and after reinstallation.
After doing a clean re-install with the 2017.02-2, there I only get the tcpdump as INFECTED, even with single test. The version of traceroute is 1.22.1, and only thing I did was an additional install of binutils and chkrootkit.
We use busybox for some tools by default.
I wonder if this checks md5sums and symlink changes are confusing it.
It’s hard to comment without knowing more about the tool, but our images are built on a secure build network with signed packages. The rootkit would have to be upstream in the Debian repositories for this to occur. This is unlikely.